Resilience is key
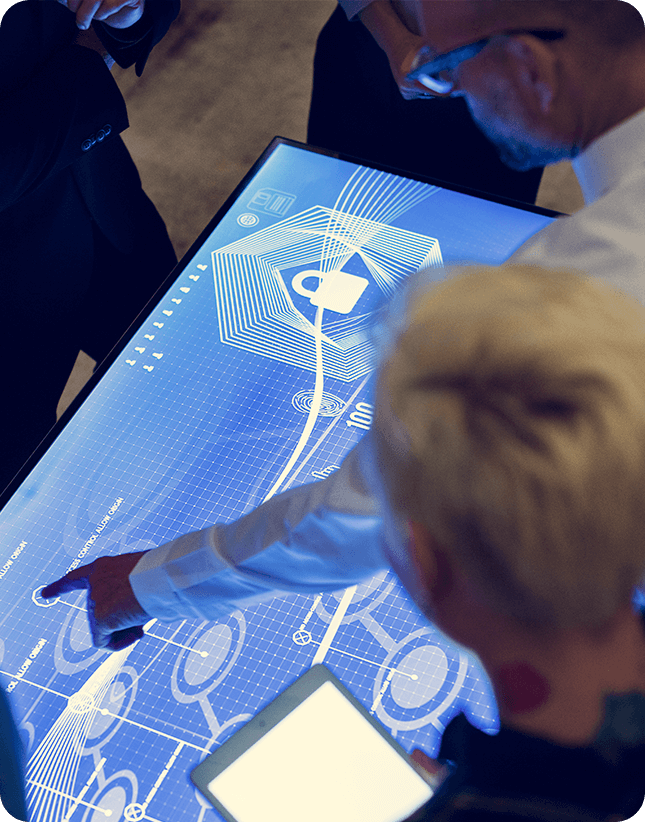
Cyber Incident Response in uncertain times
Offering Cyber Incident documentation, Crisis Exercises and Targeted Attack Discovery (Threat Hunting plus) which will assist Business Leaders prepare and respond well in a cyber crisis. We will help you prepare and respond to the direct pressures as a result of the crisis enabling the growth of your business
Download Brochure
Featured services which we provide

Documentation
We will provide you with a full suite of documents bespoke to your organisation, which will be practical and useful during an incident or crisis.
Learn more

Exercising
We offer bespoke crisis exercises specialising in cyber incidents. We have had practice over the last two years of running our exercises fully remote.
Learn more

Threat Hunting
Restricted Access Targeted Attack Discovery will be valuable if you are concerned about attacks directed towards your organisation and your industry.
Learn more
Crisis and Resilience
Collaborate in preparation to improve resilience in a crisis
It is with increasing importance that Business Leaders prepare and respond well in a crisis. We will help you prepare and respond to direct pressures as a result of the crisis enabling the growth of your business.
No crisis is the same; each can have diverse impacts that can advance rapidly, or build as the fog lifts through time. We support our clients through the challenging situations involved in the crisis while understanding that Business Leaders can feel the effects of a crisis for a prolonged period.
Our multi-skilled subject experts will dovetail with you and your team to provide professional advice to help reduce risk.
To achieve the cyber muscle memory, which will enable you to respond successfully, it is essential that crisis planning, using your document suite is a fundamental part of the preparation and integrated into business plans. When a crisis does occur, you will have exercised and tested your plan to ensure your business is resilient. We will work together with you to build trust, understand business risks, and develop strategies so that you are prepared when the inevitable happens.
Our methodology follows the National Institute of Standards and Technology (NIST) guidance on contingency planning, along with the NIST Computer Security Incident Handling Guide.
Why choose Restricted Access
How we work?


Preparation
Detection & Analysis
Containment Eradication and Recovery
Post-Incident Activity
Hear from our customers!
We cannot thank Restricted Access enough, for the Pro bono work they have carried out, both on our Cyber Incident Response Documentation and in our new and bespoke Cyber Crisis exercising programme. Our cyber maturity now leaves us with less sleepless nights.

Thank you, Restricted Access, for your input into our new Cyber Transformation programme. Your free consulting has meant that we can spend more money on what we were sent up to do; with higher confidence that we will know how to handle a cyber-attack.

Get in touch!
Just simply leave your details here and we will get
back to you within 24 hours.
Restricted Access is a proud partner of

Download all Brochures
Enquire further for information and pricing on the full suite of Heimdal products which we sell